Phishing Simulation
Phishing Simulation means that you will be phishing your own team to test the effectiveness of your phishing training. The simulated phishing emails may look like they are from a manager, vendor, or a well-known brand name. The idea is to find out how good people are at identifying these emails as fake and reporting them. Those who fail the phishing test usually get an explanation of what they can do next time to spot these phishing emails better. Know More...
Cyber 2.0'
Blocking the spread of cyber-attacks
The Mathematical Chaos Engine creates a form of chaos balance among the authorized computers. It Scrambles the Out going Traffic from the Authorized Computers and descrambles it on the computer it enters. On the other hand it doesn’t scramble outgoing traffic from the unauthorized computers and again de-scrambles it on the computer it enters. Therefore any unauthorized computer will not be able to communicate within the network, simply because it will not be conceived as such by the protected computers.
Designed in such a way that even if it is attacked or removed from the infected system, it can still protect the spread/lateral movement of the attack from the infected computer into the organization as the Cyber 2.0 agent Know More...


COVID 19-Pandemic Detection and Monitoring Technology
Covid 19 is an unprecedented situation that has turned into global pandemic and has attained an uncontrollable stage. While the research is still on to create an anti body, it's crucial that its spread is contained and prevented at the ground level and measures such as adopting Touch Free Temperature Screening technology and ensuring that people wear masks and follow social distancing norms has to be the default option.
And a Technology that combines the power of Touch Free Temperature Screening with the ability to detect temperature even with Face mask and enforced mask wearing option with audio prompts and many other top notch features are the need of the hour.
Introducing India's Most Cutting Edge COVID 19 Pandemic Monitoring & Detection Range powered by Arridae.
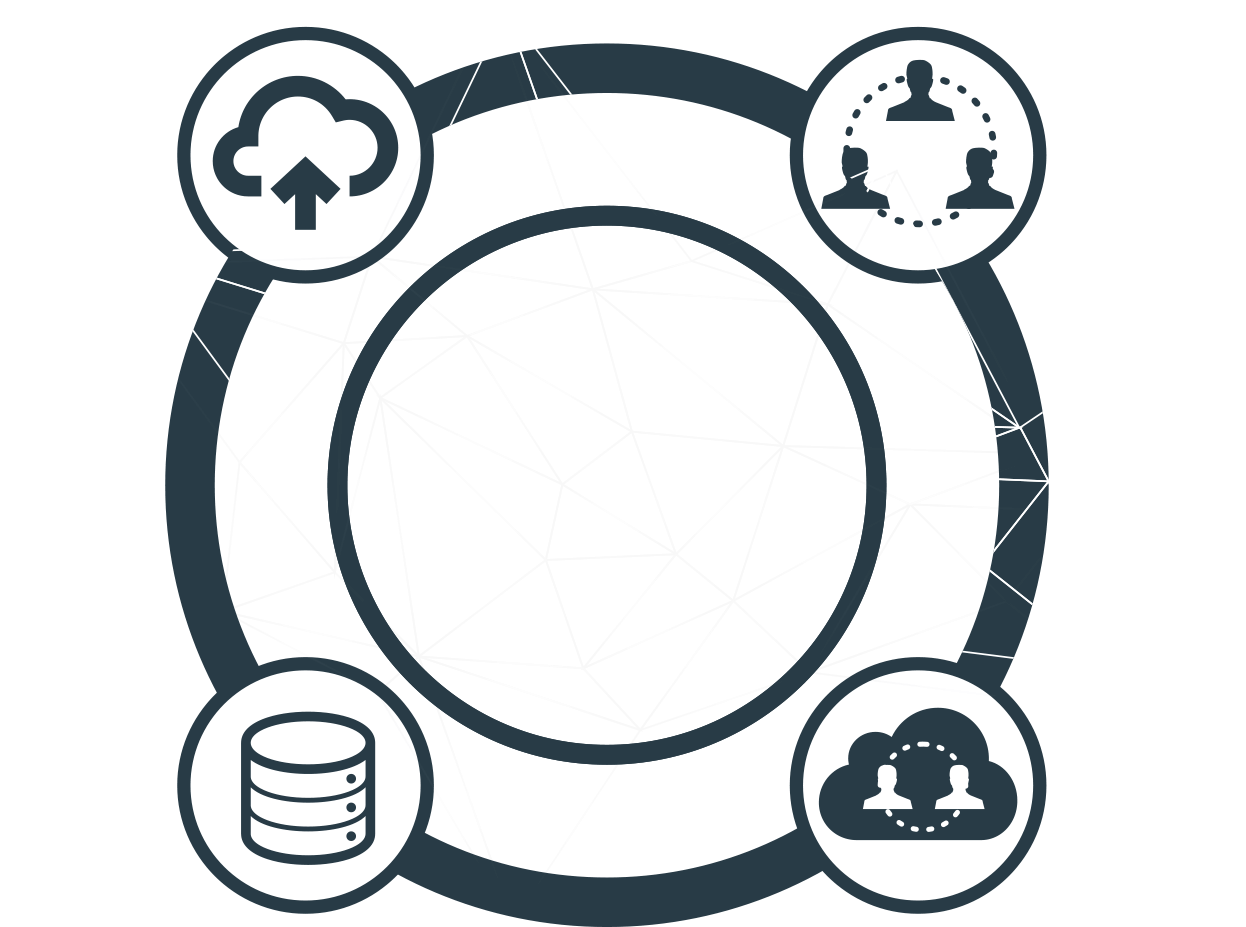
SOC as a Service (SOC)
Security Operation Center, commonly referred to as SOC, is a centralized location from where an organization’s entire IT environment is monitored to help prevent, detect and mitigate cyber-attacks. Cyber-attacks like Malware, phishing and social engineering, web-based attacks, botnets, malicious codes, and denial of service (DoS) are increasing day by day. Therefore, it became imperative to have a well-structured SOC service to help safeguard your organizations’ digital assets from these cyber-attacks. Know More...

Identity and Access Management (IAM)
Authentication services are critical for identifying and controlling user roles. By limiting and tracking employee access, you can ensure that potentially malicious users don't gain access to your computer systems.

Risk and compliance management
Companies today need to concern themselves with regulatory compliance, risk management, and security auditing. Risk and compliance management suites provide a dedicated and specialized resource to ensure this compliance.

Encryption.
Encrypted data is protected data. Even if encrypted data is stolen, it cannot be accessed. Encrypting data when it is being transferred is especially important, as otherwise it might be stolen while in transit.

Data Loss Prevention (DLP).
Most companies today rely upon their data for their critical operations. Data Loss Prevention solutions are dedicated to ensuring that data remains available and accurate.
Unified Threat Management (UTM).
A UTM solution often encompasses multiple of the above and below solutions, in a single all-around resource that is designed to both detect and mitigate threats as they come in.
Firewall
Firewalls control incoming and outgoing connections, to better protect the network from potentially malicious actions.

Antivirus/antimalware solutions
Antivirus and antimalware solutions scan a computer system looking for known threats. Modern solutions are even able to detect previously unknown threats based on their behavior.

Intrusion Detection System (IDS)/Intrusion Prevention System (IPS)
These systems work to identify any potentially hostile actions. The faster a company can identify these issues, the faster it can react to them.

Disaster Recovery
Companies have to be able to recover from a disaster quickly. Disaster recovery solutions facilitate the process of re-deploying data and requisitioning replacement resources.
Distributed Denial of Service (DDoS) mitigation.
A DDoS attack remains one of the most popular and devastating attacks on an enterprise, potentially disrupting its entire network or taking down its website. Advanced security solutions can now detect and mitigate DDoS attacks.

Web filtering
31% of data breaches are actually due to mistakes by employees. Web filtering services protect employees from accidentally accessing potentially harmful services, providing an additional layer of security regardless of their browsing habits.

NOC
The NOC is usually responsible for monitoring and maintaining the overall network infrastructure, and its primary function is to ensure uninterrupted network service.
EDR
EDR is an integrated endpoint security solution that combines real-time endpoint monitoring and collection of endpoint data with rules-based automated response and analysis capabilities.
Get complete insight into your security risk – Know more about Arridae’s Security Services
Contact Now!


